Monday, September 26, 2011
On the Subject of Privacy and Pants...
(Photo by cnewtoncom. For geek points, guess whose famous pants those are without clicking the link!)
Privacy breeches are much funnier than privacy breaches.
I'm not going to be able to get dressed tomorrow without laughing at my privacy-preserving pants. One could argue, perhaps, that the function of many pants is to provide basic privacy... but I leave the finding of non privacy-preserving pants as an exercise to the reader. And though it is a bit tempting to run a contest for the best illustration of a privacy breech breach, I imagine it would get not safe for work very quickly!
Friday, June 24, 2011
I admit, I laughed: LulzSec as popular as orgasms?
LulzSec is running around pummelling some of the world's most powerful organisations into the ground... for laughs! For lulz! For shits and giggles! Surely that tells you what you need to know about computer security: there isn't any.
While I often joke that web security is an oxymoron, they demonstrate it in the funniest ways they can find. As a web security researcher, I have to admit that their antics often make me laugh... and kinda make me wish I was allowed to use stolen data for research -- all those passwords! Data was always hard to come by when I did my spam immune system work so that much just makes me salivate a little, even if I'm pretty sure our ethics committee wouldn't let me touch it. And it's not like I do authentication research. But still! Data! I hope someone's doing cool things with it.
But here's a bit of meta-lulz: LulzSec scam discovered on Facebook - but it's not what you think. The excellent Graham Cluley discovers a Facebook scam that purports to have a picture of a LulzSec suspect, and then he sleuths out that the pixelated bait picture is, in fact, of another hacker arrested in 2008.
This means that LulzSec is apparently now so newsworthy that potential pictures of them can be used as bait for Facebook scams. They're up there with Obama, celebrity sex tapes and the ever-popular dislike button.
I don't know about you, but I got a great chuckle out of the thought that LulzSec might be as popular as orgasms... at least when it comes to scam bait.
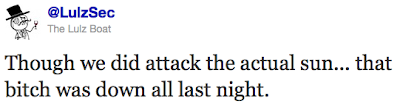
And to end with more lulz, here's my favourite LulzSec tweet of today, which came in the midst of explaining what they had and hadn't actually hacked as the media attributes everything and anything to them:
Thursday, April 7, 2011
News: Experts recommend stronger protections for "Geodata"
Currently, no consensus exists for the definition of "sensitive data" in data protection and privacy law either in the EU or the USA. However, given the status of both regions as major trading partners it is essential in the digital age that such consensus is formed soon while legislation is in a transitional period. Consistent legislation would not only protect consumers and sellers, but also improve confidence across the whole of e-commerce and mobile computing.
That's perfectly true and reasonable. But I'm less thrilled about the example of why it might be sensitive:
Jessen points out in what particular situation geo-tracking might be most sensitive. "The intrusion and loss of integrity related to the processing of geographic location data are apparent when customers are subject to constant monitoring or when geographic location data are combined with other sensitive or demographic data, such as the location of bars, casinos, red-light districts," she says. She adds that "Personal profiles are established for behavioural advertising purposes on this basis." Even anonymised location data might compromise and individual's privacy, so it too must be subsumed in new privacy legislation.
Red light districts? Once again, privacy is not just for people who have something to hide, news writers and legislators. Surely, someone can come up with some other convincing reasons for geodata to be sensitive that don't make it sound like you're protecting only compulsive gamblers, alcoholics, and others who could be conceived of as doing something not entirely socially appealing? Especially if you're then going to try to convince the US to provide consistent legislation, it seems some other examples could be helpful in making the case.
Thursday, March 31, 2011
Comprehensive Guide to Twitter Privacy: Where are you?
Comprehensive Guide to Twitter Privacy
I've become fascinated with how Twitter has such simple settings, and yet Twitter privacy is in many ways quite complex, so I'm starting to put all of this information together. This is part 2 of... a bunch.
[Part 1: Who hears what you say?]
[Part 2: Where are you?] <-- you are here!
Now read on to learn How your iPhone may be letting people know where you live and what being responsible about sharing your location really entails!
Part 2: Where are you?
A year ago, I talked about How Foursquare can help people steal your stuff. Someone had set up a handy site called PleaseRobMe.com which let you search to find out who in a given area wasn't at home based on their Foursquare checkins. (The site now says the the authors have made their point about oversharing and have disabled the search.)
The point being that while sharing your location can be a neat way to meet up with friends, it can also be used in dangerous ways. So whether it's Foursquare, Yelp, Facebook Places, Google Latitude, or Twitter, you need to think about what you're sharing and why.
Twitter's built-in location settings
At the time I wrote about PleaseRobMe.com, I don't think location was built into Twitter, but it's since been made an option for any Twitter post. I have to say, that I really love how twitter has done to make this option clear... including doing their best to make it possible to recover from an "oops" moment where you realise you've been sharing waaay too much information and want to delete all the location data to be safe:
They've also done a nice job with the "Learn more" help document, which includes the following message:Be cautious and careful about the amount of information you share online. There may be some updates where you want to share your location ("The parade is starting now." or "A truck just spilled delicious candy all over the roadway!"), and some updates where you want to keep your location private. Just like you might not want to tweet your home address, please be cautious in tweeting coordinates you don't want others to see.
That pretty much sums up the advice any security/privacy expert would give you, although the complete document also explains how to turn things on and off, when one might prefer a precise location and when one might prefer just the city, etc.
But just like with the tweet privacy settings we talked about in part 1, this isn't the only way your location can be shared. Only this time, we're not going to blame your followers... we're going to blame your camera.
How your iPhone may be telling everyone where you live
Many modern smartphones and cameras, including the iPhone, have a GPS built-in such that you can store location data with every photo. That's pretty cool when it comes to sorting photos later, but because this information is stored with a photo, each picture you share could potentially tell someone exactly where you are (or were when you took the photo).
In Cybercasing the Joint: On the Privacy Implications of Geo-Tagging, Friedland and Sommer started looking at how many people share location data, whether they did so in unsafe ways, and whether they were aware of what information they were sharing. I highly recommend you flip through their HotSec presentation to look at the examples. (Even better if you can catch them presenting -- I really enjoyed seeing that presentation in person! -- but the slides are pretty informative on their own.)
My favourite one involves William Shatner accidentally revealing a "secret" studio location when he posted about recording there! And perhaps more relevant to "cybercasing the joint" are the craigslist posts that show expensive items, their exact geolocation, and the list of times when someone will be at home to take a phone call from an interested buyer.
The issue here is that geodata is often recorded by default. And it can even be dangerous to share this information. As a parent, how would you feel if you realized your teenage daughter had been taking photos of herself in her bedroom and it turned out that any predator could figure out where she lived? How do you feel about the fact that your friends' photos from your last party may have told everyone on the internet where you live?
Many photo services, such as Twitpic and Flickr, allow you to generalize your data so that it shows up as being in a city without showing precisely where within that city. But if you choose to have it visible (or just don't hide the data), you can often get a nice map where you can zoom in:
On Flickr you can view the exif data (Exchangeable image file format -- basically extended meta-information for pictures of the photo) and get the coordinates there...
All ready for someone's stalking pleasure!
The moral of this story
Sharing your location can be scary, and protecting your location privacy doesn't stop at turning off location on Twitter or refusing to sign in to Foursquare/Facebook places/Yelp. If you don't want everyone to know exactly where you are, you also have to make sure your camera and your friends' cameras aren't giving the game away.
Stay tuned for more Twitter privacy posts in April! And in case you missed it, here's [Part 1: Who hears what you say?] which talks about tweet privacy.
Monday, March 7, 2011
Comprehensive Guide to Twitter Privacy: Who hears what you say?
Comprehensive Guide to Twitter Privacy
I've become fascinated with how Twitter has such simple settings, and yet Twitter privacy is in many ways quite complex, so I'm starting to put all of this information together. This is part 1 of... many.
[Part 1: Who hears what you say?] <-- you are here! [Part 2: Where are you?]
Note that many of the things I'm saying here are true of other social networks or any place you might share information online, but I decided this would be most readable with examples from one site, so I've decided to use Twitter, which I like and use regularly.
Part 1: Who hears what you say?
On the surface, Twitter has perhaps the simplest privacy policy of any social network:
Either everyone can read your tweets (everything you say on twitter is public) or you can make your feed private (and then maintain a list of people who are allowed to see it).
You also, regardless of which option you choose, have the option of blocking individuals from following you. Blocking someone isn't hugely effective if they can then log out and read your public feed anyhow, but it can cut down on spam.
Retweeting
Blocking everyone you don't know is not necessarily the end of the story. Just like gossip, anyone who can read what you've said can also share it. It's fairly common in twitter parlance to "retweet" a message: that is, repeat the message verbatim or sometimes with small edits for length or the addition of commentary.
When you have a public account, retweeting is pretty much harmless behaviour. Anyone could see that funny thing you said if they looked, so if one of your followers retweets it, you're really just winding up with a few more strangers seeing it than you might otherwise. But they could have looked at that tweet at any time if they so chose. Often it's a really positive thing: more people get to hear about a cause you believe in or something cool you've done.
However, the story can be quite different if you have a private account. Perhaps you have chosen to keep your account private because you and your boss don't share political views. That "funny" thing you said could become seriously awkward if she winds up seeing it retweeted. Probably you chose to make your account private for a reason, and retweets can violate your expectation of privacy.
Violating privacy with retweets?
There's actual a whole paper on this subject that appeared in Web 2.0 Security and Privacy 2010. It has the cheesy-cute title RT @IWantPrivacy: Widespread Violation of Privacy Settings in the Twitter Social Network. They found that while some clients did block users from retweeting private feeds, many didn't and of course users could always just type RT and repeat the whole message anyhow. The researchers collected 4.42 million tweets that were exposing private information in this manner, and they expect that the numbers will continue to climb.
It's hard to tell, however, whether those millions of exposed tweets were really problematic for the people who wound up exposed, however. Perhaps millions of people asked before retweeting (something you should always do before sharing private information, but I know even I forget to do this sometimes when telling a good story I heard, so I suspect retweeting is no different). Perhaps most of the tweets were cute pictures of cats that no one really minded sharing. But either way, you should be aware of what you retweet and aware of what you say that could be retweeted.
Retweeting lies
It's also worth noting that even though researchers assumed that most of those tweets were actual privacy exposures, it's equally possible that many of them were made up. If someone can type RT and your name and cut and paste in the message, there's no reason that it has to be your message that they post in. Often edits are minor, but there's nothing stopping one from going
RT @twitter we hate kittens or something significantly more damaging to someone's reputation. Without a public feed, it's hard to refute since no one can check what you said, and even with a public feed people may expect that you deleted the offending message. A recent defamation lawsuit in the US may serve as a reminder that what you say and what you seem to say on twitter could have real implications.So that little checkbox? It's clearly not the end of the story.
Stay tuned for Part 2 next week!
[Part 1: Who hears what you say?] <-- you are here! [Part 2: Where are you?]
Tuesday, March 1, 2011
News: Facebook still going to share your address/phone # with external sites
But it sounds like it's back on the table, along with an updated privacy policy format.
Given that anyone can buy a targeted Facebook advertisement, is this going to lead to new levels of stalking and general harassment from "adveritisers" who think it's totally worth a few bucks to get the phone #s of all the women who they might find attractive in their metro area? Awkward.
As usual, I recommend not having private contact information available in Facebook for your own safety.
Tuesday, February 15, 2011
To whom are you confessing?
The Office of the Privacy Commissioner of Canada isn't ready to give the app their blessing, though:
One of the selling points of the app appears to be the password-protection feature, enabling you to lock out anyone who may try to find out about your sinnin’ ways. But what seems to be missing is what Little iApps, the developer of Confession, will do with the data they collect. According to reports, the app asks users to also provide information on their age, sex and marital status – paired with detailed information on the user’s transgressions, that’s a potentially detailed profile that would be quite attractive to marketers and others.
Details on the collection and use of the user-provided data wasn’t available on Little iApps’ site…so if the developer is collecting and using information without the user knowing, does that mean they’ve broken one of the commandments themselves – “Thou shalt not steal”?
Read their entire blog post entitled ‘Fess up – where does my data go?
Monday, February 14, 2011
Free Wordpress themes considered harmful
So Why You Should Never Search For Free WordPress Themes in Google or Anywhere Else caught my eye because it's a new example of how free... sometimes isn't. Why bother to exploit people's wordpress blogs, which is illegal in many places, when you can just give them the code and let them install and run it themselves? Mostly it looks like the code found is all about adding spammy SEO-boosting links for dubious properties, but there could definitely be worse elsewhere in those themes: that free theme could be using your blog to install malicious software on your visitors' computers!
Out of the ten sites on the first page of Google, here are the stats:
Safe: 1
Iffy: 1
Avoid: 8
8 out of 10 sites included base64 encoding in their themes. The average WordPress user no doubt knows that Google isn’t the best place to find themes but the stats on these sites show that there are thousands of people downloading them and using them on their websites. Someone who has come to WordPress on the first time is more than likely to type “free WordPress themes” into Google to find a site that gives them what they want. Unfortunately they’re more than likely to end up with spammy links, at best, on their site.
Read the whole article to hear about what might be hiding in that free template you just downloaded. Basically, if you see a bunch of random encoded stuff that you don't understand, you should be awfully wary... Thankfully, the author demonstrates the use of two tools for figuring out if that theme you'd like ot try is safe: Theme Authenticity Checker and Exploit scanner. I guess those are the new antivirus for Wordpress?
Thursday, January 27, 2011
Will Facebook's choice of social authentication (face CAPTCHAs) lead to huge gains in facial recognition software?
They're calling it "social authentication" where rather than reading obfuscated text as in a normal CAPTCHA, you're asked to identify friends.
"Instead of showing you a traditional captcha on Facebook, one of the ways we may help verify your identity is through social authentication," writes Rice. "We will show you a few pictures of your friends and ask you to name the person in those photos. Hackers halfway across the world might know your password, but they don't know who your friends are."
Of course, that's not true at all. For many people with public profiles, flickr accounts, etc. it's pretty easy for a hacker to identify your friends. (Even easier if your would-be hacker is a jilted lover or angry sibling, but presumably those folk could also pass a regular CAPTCHA.) The key here isn't that this social authentication isn't hackable, though, it's that the hack has to be more carefully crafted to your account, and may well require a human to do the facial recognition necessary, thus slowing down the attack and doing exactly what CAPTCHAs were intended to do.
I'm curious to see how well it works in practice, though. CAPTCHAs in their current "mangled text" form relied on assumptions about the ineffectiveness computer text recognition... assumptions that have been rapidly broken as determined attackers and researchers have improved our text recognition algorithms. (Nowadays, many captchas can be bypassed with a higher than 90% success rate. Here's a link to one such paper but a websearch will turn up many others.)
So the interesting question to me is "Will Facebook's choice of Face CAPTCHAs lead to huge gains in facial recognition software?" -- we're well overdue for gains in that area, actually, given that law enforcement is hoping to use facial recognition to stop crime and even terrorism, but the technology is so poor right now that if they used it now they'd likely be arresting a lot of innocent folk. Facebook will lead to some great cases: What about when your friends are in costumes? Wearing different makeup? Different lighting? Different poses? Different hair?
Beyond the usual halloween costumes, my facebook friends include theatre geeks, haunted house aficionados, members of the 501st legion of Star Wars costumers and folk involved with things like the Society for Creative Anachronism. Will my friends' and acquaintances' penchant for elabourate costumes mean that I'm more secure? Or will it mean that I'll have more trouble identifying them in photos unless I've seen their standard costumes before?
Mostly I'm torn between excitement at new gains in image processing and a vague sense of unease when I contemplate the potential applications of better facial recognition software.
"My account got hacked"
Funny how people, "my account got hacked," rather than "someone hacked into my account", like they think getting hacked is an act of nature.
I had a good laugh, but it's got me wondering... given how frequently attacks occur online, maybe it really does make sense for people to conceptualize attacks as something that just happens as opposed to something more akin to "that guy robbed me." Makes it easier to deal with somehow, or perhaps easier to accept that there will likely be no retribution?
And more disturbingly, does this "act of nature" approach to hacking explain the general public's sometimes apathetic response to routine privacy violations, both online and offline?
Wednesday, January 26, 2011
Zuckerberg... hacked?
Obviously, Zuckerberg didn’t actually write it. Or at least, we’re pretty sure he didn’t. Instead, it would appear that his fan page was hacked. Facebook has now taken down the page — but not before we grabbed a screenshot.
Honestly, these things happen. But what made the story actually funny to me was this tweet:
@snipeyhead Hah. FB is flagging the Tech Crunch article reporting on Zuckerberg's fan page hack as "abusive or spammy" http://twitpic.com/3thf68 #classy
Edit: More news on what happened according to Facebook: Facebook blames bug for Zuckerberg page hack
Ethical hacking? How about some ethical writing?

Now, I haven't verified this at all, but here's an interesting link for you: Ankit Fadia / Manu Zacharia - "Network Intrusion Alert" Heavily Plagiarized.
An extremely detailed analysis has been performed for the first chapter (10 pages) to show the scope and method of plagiarism. Our analysis shows that roughly 90% of the first chapter, including the six graphics used, has been taken from other sources. Due to time constraints, notes are used for brevity for the rest of the material.
Given my experiences with plagiarism among my undergraduate students and the recent Cooks Source plagarism story (which attracted quite a lot of attention)... I'm sadly inclined to believe that this entire book may be plagiarized.
What's funny about this story is that the book in contention here is titled "Network Intrusion Alert: An Ethical Hacking Guide to Intrusion Detection." Emphasis mine.
Monday, January 17, 2011
Facebook now enabling annoying phone calls and paper junk mail?
Now, part of me wants to just shrug: it's always been technically possible for third party developers to get access to this information because of the current state of web security. It's long been true that anyone who can execute JavaScript in your browser on a site (e.g. every facebook app) can gain access to anything you can see. So if your friend installed FarmVille and you've allowed your friend to see your phone number, FarmVille can see your phone number (and the pictures of you in that horrible halloween costume, and that drunken post you made on your ex's wall...). And if you install FarmVille, they can even more easily glean your phone number and anything else on your profile. What Facebook's doing is in some ways good: they're helping to make this clear to users, and maybe even helping to track who is actually looking at and using that info.
But of course, most people aren't aware that this has always been possible, so they're suddenly envisioning FarmVille sending them paper brochures filled with new crop info, or phoning all their friends to ask why they haven't helped out on the farm lately. Maybe an automated call would help convince you to join the game and seek out that lost kitten?
And maybe those third party apps didn't realize they could do it either, and they're salivating over the extended marketing possibilities. Technically possible doesn't imply endorsed by Facebook the way putting the ability into the API does, so while getting this information might have been in the realm of sketchy scams before, now it's going to be considered a legitimate asset by more companies. After all, you consented when you installed the app. And remember, corporate assets do tend to be about making money, so don't assume they won't sell those lists.
So, while it was technically feasible before, maybe now is a good time to reconsider what data you keep within Facebook. And it's always a good time to re-evaluate which applications you have installed or will install. As always, I recommend that you don't leave anything on facebook you wouldn't want shared with the world, so now's a great time to delete your phone number and address from your facebook profile. And if you don't? Well, don't be too surprised when you start getting texts saying that someone needs help with their FarmVille crops.
Monday, January 3, 2011
A bit late: Santa's privacy policy
Santa Claus requires your information in order to compile his annual list of Who is Naughty and Who is Nice, and to ensure accuracy when he checks it twice. Your information is also used in connection with delivering the kinds of goods and services you've come to expect from Santa, including but not limited to toys, games, good cheer, merriment, Christmas spirit, seasonal joy, and holly jollyness.
Read the rest here: "Santa's Privacy Policy" and leave those christmas decorations up just one more day before getting back to regular old January.