How can you stay safe and keep things private while still taking part in online life? I'm a web security researcher, so I get asked this fairly frequently. And it's easy to see how people get overwhelmed by all the
news stories, the marketing blurbs, and the
constantly changing policies.
Why I'm not telling you to quit Facebook
Let's say you're worried about your risk of getting into a car accident. Do you sell your car and refuse to get into any moving vehicle? No. Refusing to use a car might make you safer, but it would be quite isolating and, depending on where and how you live, very difficult. Just like many people live without cars, you can live without social networking, but it there are some significant costs to refusing to participate. Many people's need or desire to participate is much stronger that the risks they face.
If you're worried about car accidents, you've got other options to manage your risks than giving up your car. You can learn to drive defensively. You can make sure you wear your seatbelt. You can learn about the safety ratings and use cars that perform better in safety tests. You can refuse to drive places that are dangerous.
So what I'm hoping to do here is give you a crash course in the social media equivalent of defensive driving.
The web is not a safe place
When I learned to drive, my driving instructor often reminded me that I had to treat every car on the road as if it were being driven by a moron who might swerve into my lane at any time. It might seem like a very negative point of view, but it's a very practical one that's helped me avoid accidents on numerous occasions simply because I was expecting it.
My blog is called
Web Insecurity for a reason.
Nearly 2/3 of web pages currently have a serious vulnerability. So that means no matter what the policy is, how careful you are, or how careful your friends are... there's a good chance you are going to view some code controlled by a bad guy, and they could get information about you that you don't want them to have. It's often very easy to exploit these vulnerable parts of a website. 75% of websites with malicious code are legitimate sites.
You may be thinking, "sure, but no one's going to care about
my data." And you may be right. But if a bad guy is trying to make a company look terrible, one way to do so is to expose information about all of their users. You can definitely wind up as collateral damage.
Learn your legal protections
Remember that things that may seem similar often have very different legal protections. For example, if my credit card number is stolen, there are
laws that limit my liability to $50. But that's not true about all money transactions online: Debit/bank cards have no such legal protection. Some modern credit cards that require a PIN have no such protection
even though these cards aren't actually safe. You may have no legal protection from your bank if you don't follow their security procedure to the letter, and those
security requirements of online banks can be pretty crazy: Do you reboot your computer every time you bank? No? You might be on the hook if someone compromises your account!
So yeah. It's a bit of work, but it's worth it to at least learn about the issues that affect you.
Learn the controls
It may seem a bit silly, given that I've already told you that websites can easily be compromised, but if you're managing risks you should learn to use your privacy controls, choose good passwords and security questions, and keep those things private. Again, it's about managing your risks: even if these controls can't make you 100% safe, they might make you safer.
Companies are not your friends
For many companies online, you are not really their primary customer: your time and your personal information are assets the company sells to their advertisers. You have to expect to be treated accordingly. You have to
treat every company or organization you interact with online as potential hazards. Many companies intentionally or unintentionally
violate privacy laws and even
violate their own privacy rules. And privacy rules change, sometimes because the company itself changed them, sometimes because they get bought out by another company. Your guarantee when you signed up for the site is unlikely to hold a year from now, but it may be nigh impossible to remove your data from the system when it changes.
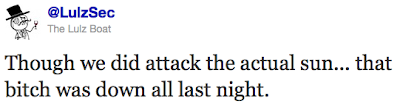
And that's just the "legitimate" problems that could affect you: there's a good chance any company's sites could be attacked and your data exposed as a result -- it happens to fully legitimate companies all the time, no matter how good their intentions towards you and your data.
Choose your friends wisely
You wouldn't tell all your secrets to the office gossip, but online your friends may be "forced" to become gossips either through malicious software or through changing policies. It sounds like some crazy super-spy movie: trust no one! Your friends could be compromised! But once again, just like I'm not telling you to delete your facebook account, I'm not going to tell you not to share, just to be defensive.
For example, I have a couple of friends who really enjoy Facebook games. They seem to install every new thing that comes along and invite me to join. Nothing wrong with that, right? I mean, if I don't want to join, I just don't, and that's the end of it. Except that it's not: my friends have all these games and thus all these extra ways that someone might break in to their accounts. And indeed, these are the folk who wind up with compromised accounts more often than most. So while these are great people who I'd be happy to share job concerns or relationship woes with in real life... It's too risky for me to share private stuff with them online. They are the office gossips, whether they mean to be or not. They're not the only ones who put me at risk (any friend can end up on the wrong end of a broken website) but they're the riskiest.
Choose what you want to share
The biggest part of managing your risk is choosing what you want to share online. Here's a few questions you might want to ask yourself:
- Will this embarrass me if it gets out?
- Will this affect my safety?
- Will this affect my employment?
- Will this affect my family/friends?
You have to assume that anything you share online could become public knowledge. You can't trust the companies, you can't assume their sites are safe, and you can't even trust your friends because of unsafe websites.
Think before you share.
One other way to manage risk is to use a pen name or pseudonym. Lots of people do this to give them a layer of privacy, especially when trying out something new like starting a silly blog, or when engaging in discussion that could be sensitive such as online political debate. Sometimes it's even an open secret that so-and-so goes by a nickname online, and the only reason they do is to make it harder for potential employers to come up with a list of everything they do online when searching their legal name and given email address.
This is a great tool if you want some more freedom to speak, but people sometimes will do the legwork necessary to figure out who you are, especially if you're high-profile or saying something unpopular. So pen names are great, but do remember that they're not 100% guaranteed to keep you safe. Again, it's another way to manage risks.
No matter what you do, everything may become public
I've said this a bunch of different ways, but this is the real take-home message here: No matter how careful you are, anything you do online can become public knowledge. It's up to you to manage your risks accordingly.
But don't despair -- it may sound stupidly hard, but you're already handling issues of trust and privacy every time you choose to tell a story to a friend or complain about work at a party. You might have to pretend you're in a spy movie and trust no one, or you might decide some things are perfectly fine to share with the world. Just try to make an informed decision.